Open-source software gets better and is more secure when trust and cooperation win out over secrecy and working alone in the dark. Patchstack’s report on the State of WordPress Security in 2022 shows this is not just an ideal but an achievable reality. Transparency and collaboration on security issues play to the strengths of open-source communities. They’re essential values and practices for building and maintaining better — and more secure — WordPress sites, products, and services. We’re proud to have Patchstack as a partner delivering the latest vulnerability information to our iThemes Security and Security Pro customers so they can better protect all the WordPress sites they build, own, or manage.
Patchstack, a leading open source security research firm and CVE Numbering Authority (CNA), has released its annual report on the State of WordPress Security in 2022. This report includes but goes far beyond the usual analysis of security trends. It shows the impact Patchstack is having with its unique bug bounty program, the Patchstack Alliance. This cooperative, voluntary, and open network is helping WordPress developers discover and patch security bugs every day. Those patches turn into security alerts and updates the WordPress community relies on. Our iThemes Security and Security Pro users receive a 48-hour advance notification when a new vulnerability impacts their site, thanks to Patchstack. Many of the security updates that we all routinely apply to our WordPress sites will be at least partly the result of Patchstack’s pioneering work.
Disclosing Vulnerabilities Makes the WordPress Space Safer
Patchstack’s database showed a 328% increase in reported vulnerabilities in 2022. They explain this spike as a result of security researchers “looking harder and farther” into code all across the WordPress ecosystem. Detecting more vulnerabilities indicates WordPress is getting safer, Patchstack believes. Other findings in their State of WordPress Security in 2022 support this conclusion. For example, the vulnerabilities discovered (and quickly patched) in some of the most widely used WordPress plugins (e.g., Elementor, Yoast, All-in-One SEO, MonsterInsights, Wordfence) were not the target of the most active exploits.
The Challenges of Unpatched Vulnerabilities and Broken Supply Chains
By Patchstack’s analysis, the biggest targets for active exploits in the WordPress ecosystem are plugins with known vulnerabilities that go unpatched, sometimes for years. In a spot check of all sites monitored by Patchstack’s network, an average of 42% were running a known insecure component. Unpatched plugins account for 26% of the most critical security bugs reported in 2022 — a number we’d all like to see trending downward. The Patchstack Alliance works toward that goal with developers to help patch newly discovered vulnerabilities, but this isn’t possible with abandoned software.
[pullquote]One of the most important trends noted in Patchstack’s annual report links an upswing in CSRF vulnerabilities to their propagation across many sites through a single dependency.[/pullquote] While Cross-Site Scripting (XSS) vulnerabilities remain common, Cross-site Request Forgery (CSRF) bugs trended higher in 2022. Patchstack reports this was due partly to CSRF bugs that surfaced in both the YITH and Freemius frameworks, underscoring the importance of maintaining supply chains with all downstream users of a common codebase.
In 2023, as we follow Patchstack’s data in our weekly vulnerability reports at iThemes, we’re seeing three times as many XSS vulnerabilities compared to CSRF reports. That’s a good sign that 2022 was an outlier. As we noted in our own 2022 security report, it’s also good news that most vulnerabilities last year were in the low-to-medium risk categories for their severity. Patchstack’s data shows these less severe vulnerabilities made up 87% of the total in 2022.
End Users Deserve Accessible and Actionable Vulnerability Data
Severity ratings are one thing, but actually understanding whether and how a vulnerability affects your site is a different story. Many CNAs and their vulnerability databases are highly technical in how they document each vulnerability. WordPress users need to know, in terms they can easily understand, just how exposed they may be when vulnerabilities emerge. The Patchstack vulnerability database aims to provide that information to any site owner so they can understand threats and take appropriate action. And that information powers our iThemes Security product.
Here is a typical Patchstack vulnerability description for CVE-2023-0968 (MITRE) in the Patchstack database:
Marco Wotschka discovered and reported this Cross-Site Scripting (XSS) vulnerability in WordPress Watu Quiz Plugin. This could allow a malicious actor to inject malicious scripts, such as redirects, advertisements, and other HTML payloads into your website which will be executed when guests visit your site.
WordPress and iThemes Security or Security Pro users with an insecure version of this plugin installed on their site will receive an alert. They also have the option to read more about the potential risks the vulnerability may pose for them. Significantly, Patchstack rated CVE-2023-0968 as a high-severity vulnerability in contrast to other CNAs. Others didn’t note attackers can exploit this vulnerability without a user account or privileges on the targeted site — a crucial detail.
CNAs May Differ Significantly in How They Assess and Describe Threats
As you can see in the example above, Patchstack gives credit to the security researchers who are key to finding and patching vulnerabilities before they can be exploited. They deserve it! The end user or site owner receiving these alerts also deserves clarity about the risks they face. Patchstack’s summary makes it clear where the threat lies. Clicking through to the technical details in their database confirms this vulnerability can be exploited without logging into the site. This is the clarity in communication and positive user experience you can expect if you are an iThemes Security or Security Pro user.
Devin Walker, General Manager of StellarWP, said he is proud to be a part of Patchstack’s network since partnering with them earlier this year and adopting their vulnerability database for iThemes Security users. In his view, [pullquote]”Patchstack’s comprehensive security report highlights their commitment to actively identifying and addressing security vulnerabilities in the WordPress ecosystem. By being transparent about their work, they are setting the standard for how security should be approached in the industry.”[/pullquote]
Nipping Bugs in the Bud — The WordPress Way
Patchstack doesn’t just report bugs others bring to light — they find bugs and help fix them. No one is looking harder and farther into WordPress security issues than the Patchstack Alliance, which is open to anyone working in open source security.
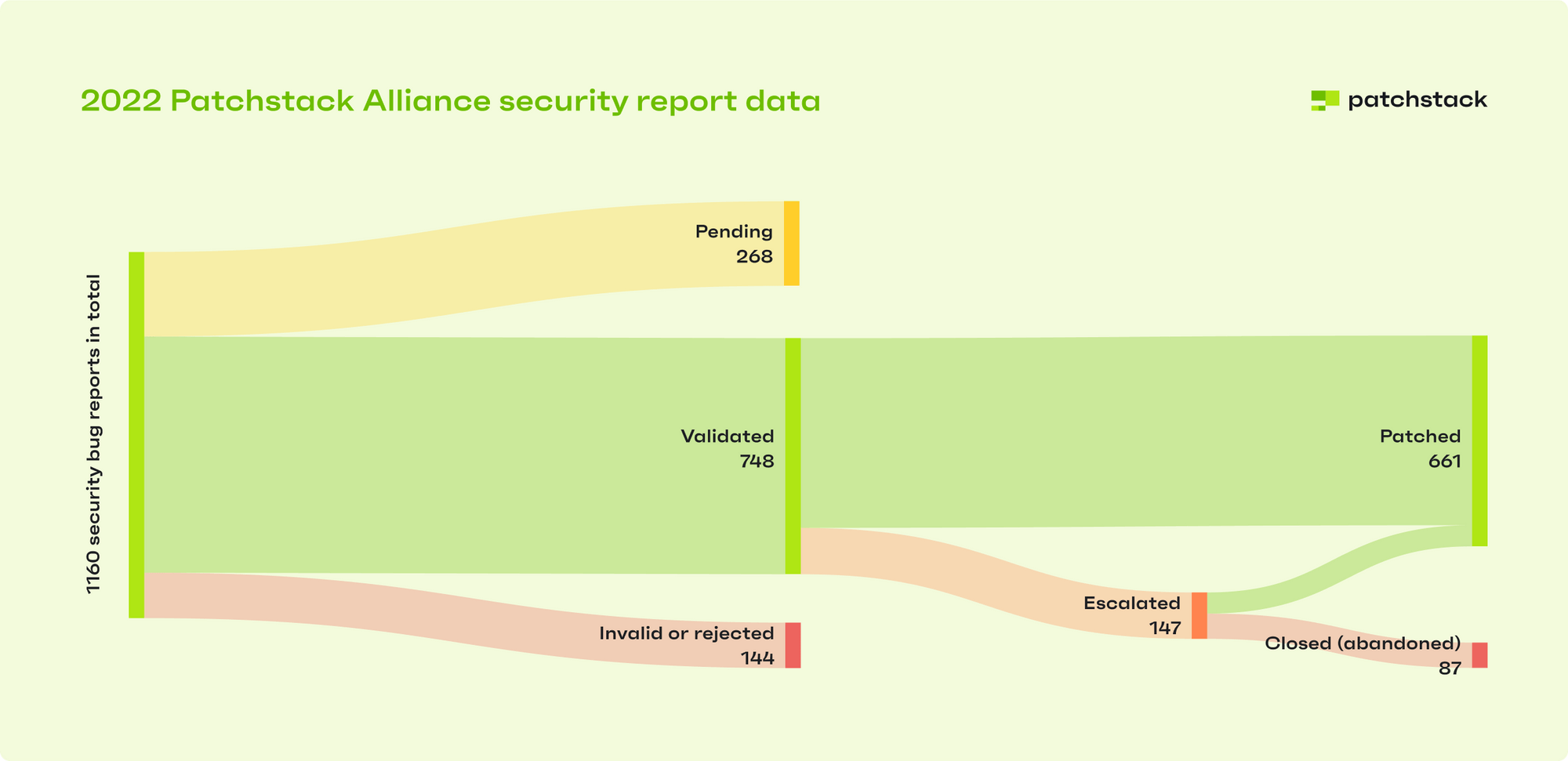
In 2022, Patchstack paid $16,050 in bounties to ethical hackers in their network. These researchers discovered and verified 748 unique security bugs in the WordPress ecosystem. That’s only $21.46 to nip a bug in the bud! It’s far, far less than what it would cost to deal with the same bug as a zero-day exploit.
Out of the 748 validated bug reports, Patchstack was able to see 661 through to patches by working with the people responsible for the vulnerable code. Only 147 or 20% of these cases had to be escalated to the WordPress plugin team.
Patchstack partners with 17 hosting and service providers (including iThemes) to proactively warn and protect their customers when they are using insecure software. Some, like One.com, have successfully patched their own customers’ sites — a practice that may be helpful for other hosts to adopt.
WordPress Security is a Community Effort
Patchstack CEO Oliver Sild says what makes his company unique is a driving focus on transparency and community. “We talk about vulnerabilities as they are without using them for fearmongering, and we make sure security researchers who contribute to finding issues in open source will be as valued as developers who build these projects,” he said.
Another key difference in the security space is Patchstack’s emphasis on collaboration. Oliver says they will work with anyone who can help make a positive impact, including others in the security space. Competition can coexist with cooperation, and when it comes to vulnerabilities in open source, it’s critical to come together on common interests like security. This cooperation delivers peace of mind to our iThemes Security and Security Pro users. Our customers can be confident they are getting clear, actionable, and timely alerts about new vulnerabilities 48 hours before they are openly publicized. And that is thanks to our partners at Patchstack, along with everyone else supporting their initiatives and working together to secure the WordPress ecosystem.
Solid Security is part of Solid Suite — The best foundation for WordPress websites.
Every WordPress site needs security, backups, and management tools. That’s Solid Suite — an integrated bundle of three plugins: Solid Security, Solid Backups, and Solid Central. You also get access to Solid Academy’s learning resources for WordPress professionals. Build your next WordPress website on a solid foundation with Solid Suite!
Sign up now — Get SolidWP updates and valuable content straight to your inbox
Sign up
Get started with confidence — risk free, guaranteed