How secure is WordPress? Against a backdrop of steadily increasing global cyberattacks and sophisticated cybercrime targetting more than half of all small to mid-sized businesses (SMBs) in North America, WordPress’s dominant global CMS market share (60%+) presents a large attack surface to hackers and cybercriminals whose tools now include artificial intelligence and machine learning. Every year, the number of new vulnerabilities increases in the WordPress ecosystem, and 2022 was no exception. What have we learned from the data this time?
What counts as a vulnerability?
First of all, it’s important to understand how software vulnerabilities are assessed.
Vulnerabilities are not exploits. They are theoretically exploitable attack surfaces, but without an active exploit or working proof of concept, it’s often not clear whether they represent a significant risk. Security analysts often use the Common Vulnerability Scoring System (CVSS) to rate vulnerabilities on a 0-10 scale, indicating their severity. These scores vary across the tech industry because the potential impact of a particular vulnerability can’t be generalized. A vulnerability is more or less severe in its potential impact on particular systems, services, or products. We followed WPScan‘s scoring which is aligned with the WordPress platform and ecosystem.
We also used WPScan’s vulnerability tracking and risk assessment in 2022 and the previous years to produce our weekly vulnerability report. For 2022, the WPScan database recorded 23 vulnerabilities for WordPress core. Other security analysts may take a broader or narrower view of what counts as a vulnerability.
For example, Patchstack’s vulnerability database for WordPress includes 27 core vulnerabilities for 2022, and they’ve verified 15 as exploitable. In contrast, only nine core vulnerabilities were reported to MITRE and recorded in the National Vulnerability Database with a Common Vulnerability and Exposure (CVE) identifier. The details of a CVE, like its severity rating, can be revised over time. A CVE can even be canceled. Unusually, an additional core WordPress CVE was rejected as a false positive in 2022.
Moving forward in 2023, we are using Patchstack to track vulnerability data, report on it in our weekly security newsletters, and power iThemes Security and Security Pro’s Site Scan vulnerability detection feature.
2022 WordPress Vulnerability Trends
- 2% of all plugins were the source of 99% of the total vulnerabilities.
- Every week, vulnerabilities surfaced in 20-50 plugins and themes.
- Each month, an average of 121 plugins and themes had a vulnerability publicized.
- The severity of vulnerabilities declined significantly compared to 2021.
- 26% of the plugin and theme vulnerabilities were unpatched at the time of their disclosure.
- XSS vulnerabilities were the most prevalent, followed by CSRF and SQLi.
- XSS, CSRF, and SQLi vulnerabilities represented 73% of all vulnerabilities.
WordPress core security is solid.
Fortunately, the vulnerabilities that came to light in WordPress core in 2022 were discovered and quickly fixed by members of the WordPress security team and other researchers who were proactively looking for them. Their diligent efforts led to four WordPress security releases in 2022 that patched 20-30 potential vulnerabilities, depending on how they are classified. The WordPress 6.0.3 security release patched 16 of these all in one go.
Select plugins and themes carefully — and keep them updated!
Of those potential vulnerabilities, none posed an immediate risk to WordPress users. That is also true of the one remaining unpatched vulnerability in core that emerged in mid-December when security researchers publicized a known issue with WordPress’s pingback feature. A patch may be in the works for a future security or maintenance release, but there is no immediate cause for concern. To be exploited, a second vulnerability would also have to be exploited and the targetted site’s DNS service — typically a host or domain registrar — would also need to be compromised. This rare and extreme condition would be very damaging in its own right.
We have provided further details and guidance about eliminating this vulnerability now by turning off XML-RPC. This is always a good idea if you’re not using it.
Two percent of WordPress plugins are responsible for 99% of the vulnerabilities.
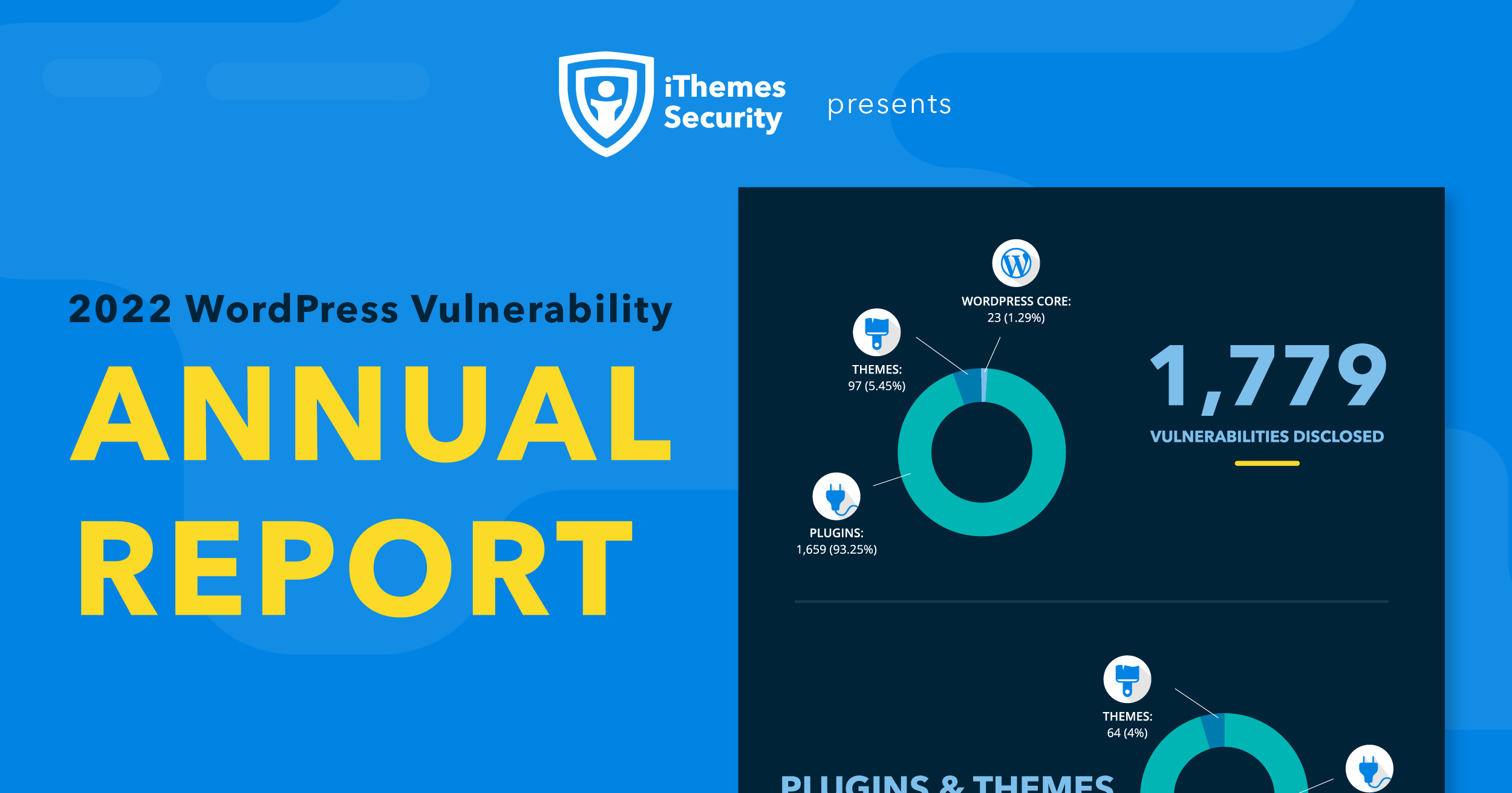
In the 2022 vulnerability data we present here, 23 core vulnerabilities represent 1% of the total number of vulnerabilities we tracked (1,779) in 2022. That means plugins and themes are responsible for 99% (1,756) of all vulnerabilities. This is consistent with last year when we tracked 1,628 vulnerabilities, 98% of which were linked to plugins.
In a typical week, 30-40 individual plugins and themes saw at least one vulnerability surface.
This is not entirely a bad thing, however. We would not want to see significantly more vulnerabilities in core or themes. Plugins are the largest and most attractive attack surface in the WordPress ecosystem, but the vast majority of them are not associated with a publicly disclosed vulnerability in any given year.
For context, the number of individual plugins and themes that experienced a vulnerability week-to-week in 2022 (1,425) represents about 2% of the total pool of 70,000+ available at wordpress.org. Of course, not all WordPress plugins and themes are hosted there, but the vast majority are. Within the total universe of WordPress add-ons, we can say less than 2% of them introduced 99% of the vulnerabilities tracked in 2022.
Looking ahead, this is a statistic we can hope to see in decline thanks to the work of the WordPress Security, Performance, and Core teams. A proposal to help plugin developers and the plugin review team raise standards and assess plugins with a plugin checker is especially promising.
All WordPress Vulnerabilities By Source
| Vulnerability Source | Number Reported | Percentage of Total (1,779) |
|---|---|---|
| WordPress Core | 23 | 1.29% |
| Theme | 97 | 5.45% |
| Plugins | 1,659 | 93.25% |
On any given week, 20 to 50 individual plugins and themes experienced at least one vulnerability in 2022. We saw a monthly average of 121 individual plugins and themes that had at least one vulnerability emerge.
To make it easier to see trends, we’ve removed one outlier event in the first week of March 2022 from our tables and charts: the Freemius SDK framework vulnerability. This can be counted as one vulnerability in a plugin dependency — or as 400+ plugins and 25 themes that all contain the vulnerable Freemius code.
WordPress Plugins and Themes With One or More Vulnerabilities, Month-by-Month
| Month | Plugins | Themes | Total |
|---|---|---|---|
| January | 116 | 0 | 116 |
| February | 109 | 41 | 150 |
| March | 114 | 0 | 114 |
| April | 101 | 1 | 102 |
| May | 129 | 3 | 132 |
| June | 125 | 0 | 125 |
| July | 82 | 3 | 85 |
| August | 122 | 2 | 124 |
| September | 88 | 1 | 89 |
| October | 65 | 2 | 67 |
| November | 161 | 6 | 167 |
| December | 149 | 5 | 154 |
| Total | 1,361 | 64 | 1,425 |
| Average | 113 | 5 | 121 |
2022 saw medium to low-risk ratings for 70% of all the vulnerabilities we tracked. Only 4% were rated critical. You can also look at it in the other direction: 75% of all vulnerabilities were rated medium to high severity — that’s significant. However, it’s also a significant decline in threat levels compared to 2021. In 2022 we see a downward shift of 18 percentage points from critical and high to medium and low. Critical vulnerabilities dropped from 8% in 2021 to 4% while low-threat vulnerabilities rose to 21%, up from 11% in 2021.
All WordPress Vulnerabilities By Threat Level, Year-to-Year (2021-2022)
| Year | Critical | High | Medium | Low |
|---|---|---|---|---|
| 2022 | 74 (4%) | 446 (25%) | 894 (50%) | 365 (21%) |
| 2021 | 137 (8%) | 630 (39%) | 678 (42%) | 183 (11%) |
All WordPress Vulnerabilities By Threat Level, Month-to-Month (2022)
| Month | Critical | High | Medium | Low | Total |
|---|---|---|---|---|---|
| January | 10 | 50 | 73 | 14 | 147 |
| February | 14 | 33 | 108 | 14 | 169 |
| March | 5 | 111 | 27 | 16 | 159 |
| April | 6 | 51 | 40 | 23 | 120 |
| May | 4 | 22 | 87 | 42 | 155 |
| June | 5 | 12 | 107 | 27 | 182 |
| July | 2 | 14 | 55 | 36 | 107 |
| August | 4 | 28 | 96 | 30 | 158 |
| September | 8 | 7 | 72 | 24 | 111 |
| October | 3 | 13 | 44 | 18 | 90 |
| November | 7 | 26 | 107 | 59 | 199 |
| December | 6 | 78 | 49 | 49 | 182 |
| Total | 74 (4%) | 446 (25%) | 894 (50%) | 365 (21%) | |
| Average | 6 | 37 | 75 | 30 |
Up from 337 (23%) last year, 2022 saw 456 (26%) vulnerabilities remain unpatched at the time they were publicly disclosed. Of course, that’s not what we want to see.
WordPress Plugin Vulnerability Status at Time of Disclosure (2022)
| Status | Number Reported | Percentage of Total (1,779) |
|---|---|---|
| Patched | 1,231 | 69% |
| No Known Fix | 456 | 26% |
| Plugin Closed | 92 | 5% |
WordPress core is solid. It’s what you add to it and how you maintain the whole system that may make it vulnerable to security threats. But if you make timely updates, limit user access appropriately, add multifactor authentication — and choose your plugins wisely — your WordPress site will be solid from tip to toe.
Unpatched vulnerable plugins are just as bad as plugins with a patch that has not been applied with a simple update. These are the most vulnerable targets. If 2022’s trends continue they’re most likely to fall victim to XSS and CSRF attacks if current trends continue. Together these attack methods account for over 65% of all WordPress vulnerabilities that surfaced in 2022.
Notably, CSRF vulnerabilities increased by 5%, which is consistent with reporting from other sources in and beyond the WordPress ecosystem. As a subset of brute-force login attacks, credential stuffing is also increasingly prevalent as hackers test stolen login credentials. There’s no software vulnerability at work in credential stuffing with stolen passwords apart from the targeted users who aren’t using multifactor authentication — or even better, a passwordless login.
Top WordPress Threat Vectors, Year-to-Year (2021-2022)
| Threat Vector (Vulnerability Type) | 2021 | 2022 |
|---|---|---|
| Cross-Site Scripting (XSS) | 885 (54.4%) | 890 (50%) |
| Cross-Site Request Forgery (CSRF) | 167 (10.2%) | 261 (14.7%) |
| SQL Injections | 152 (9.3%) | 142 (8%) |
| Bypasses | 68 (4.2%) | 28 (1.6%) |
| RCE Vulnerabilities | 20 (1.2%) | 23 (1.3%) |
| PHP Vulnerabilities | 19 (1.2%) | 31 (1.7%) |
| Var Disclosures | 19 (1.2%) | 26 (1.5%) |
| Sensitive Information Disclosure | 6 (0.4%) | 16 (0.9%) |
| Server-Side Request Forgery (SSRF) | 0 (0%) | 13 (0.7%) |
| REST API | 11 (0.7%) | 5 (0.3%) |
| All Others | 281 (17.3%) | 344 (19.3%) |
| Total | 1,628 | 1,779 |
Responsible disclosure is the right thing to do — even when it hurts.
In 2022, our weekly security reports called attention to several popular plugins, including one of our own, with vulnerabilities potentially impacting very large numbers of websites.
There’s no software vulnerability at work in credential stuffing with stolen passwords apart from the targetted users who aren’t using multifactor authentication — or even better, a passwordless login.
- As noted above, over 400 plugins and themes using the Freemius framework were affected by a single vulnerability, but most were patched or removed from the wordpress.org repositories.
- More than 5 million Elementor users experienced a critical vulnerability that was quickly patched.
- Another million Ninja Forms users received a forced update from WordPress.org, an unusual step taken by the security team due to the critical nature of the vulnerability.
- Finally, BackupBuddy patched a high-severity vulnerability and made it available to all users, even if they had expired licenses, and the updated version was pushed automatically to our Sync users.
This information needs to get out once plugin and theme developers have patched vulnerabilities and are ready to release a security update. That all needs to happen as quickly as possible, and generally it does — within the professional WordPress marketplace where there’s a lot of cooperation and partnerships around common interests like security. As an end user, your role is to apply updates, support any customers or clients you have that may be affected — and spread the word about all new releases — especially those with critical security updates.
Run — do not slow-walk — your updates!
All our findings in this report repeat the trends of previous years and underscore the importance of keeping your WordPress site up to date. To be exploited, many vulnerabilities would require an attacker to have access to a WordPress user account with elevated privileges, but this points to the need to harden your user authentication security and periodically review your users. Always apply the principle of the least privilege — no one needs to have higher permission levels than necessary.
WordPress core is solid. It’s what you add to it and how you maintain the whole system that may make it vulnerable to security threats. But if you make timely updates, limit user access appropriately, add multifactor authentication — and choose your plugins wisely — your WordPress site will be solid from tip to toe.
Solid Security is part of Solid Suite — The best foundation for WordPress websites.
Every WordPress site needs security, backups, and management tools. That’s Solid Suite — an integrated bundle of three plugins: Solid Security, Solid Backups, and Solid Central. You also get access to Solid Academy’s learning resources for WordPress professionals. Build your next WordPress website on a solid foundation with Solid Suite!
Sign up now — Get SolidWP updates and valuable content straight to your inbox
Sign up
Get started with confidence — risk free, guaranteed