WordPress Hacked? 7 Warning Signs To Watch
One of the most frustrating and stressful situations you could ever run into as a WordPress site owner is finding out that your site has been hacked. One minute your site is humming along, bringing in traffic and, hopefully, revenue. And then, next thing you know, you discover something is very wrong with your WordPress site.

One of the most frustrating and stressful situations you could ever run into as a WordPress site owner is finding out that your site has been hacked. One minute your site is humming along, bringing in traffic and, hopefully, revenue. And then, next thing you know, you discover something is very wrong with your WordPress site.
Unfortunately, the reality that your WordPress site could be hacked needs to be dealt with as efficiently and effectively as possible to make sure it never happens. Because if you find yourself facing a hacked website, you’ll probably be asking yourself why your site, in particular, was the target of a malicious attack and how to get it back as quickly as possible.
WordPress hacks come in many forms, shapes, and sizes. This means, as WordPress site owners, it’s important to know all of the common reasons why WordPress sites can be successfully hacked. In this guide, we’ll discuss the common reasons WordPress sites get hacked along with simple steps you can take to secure your site.
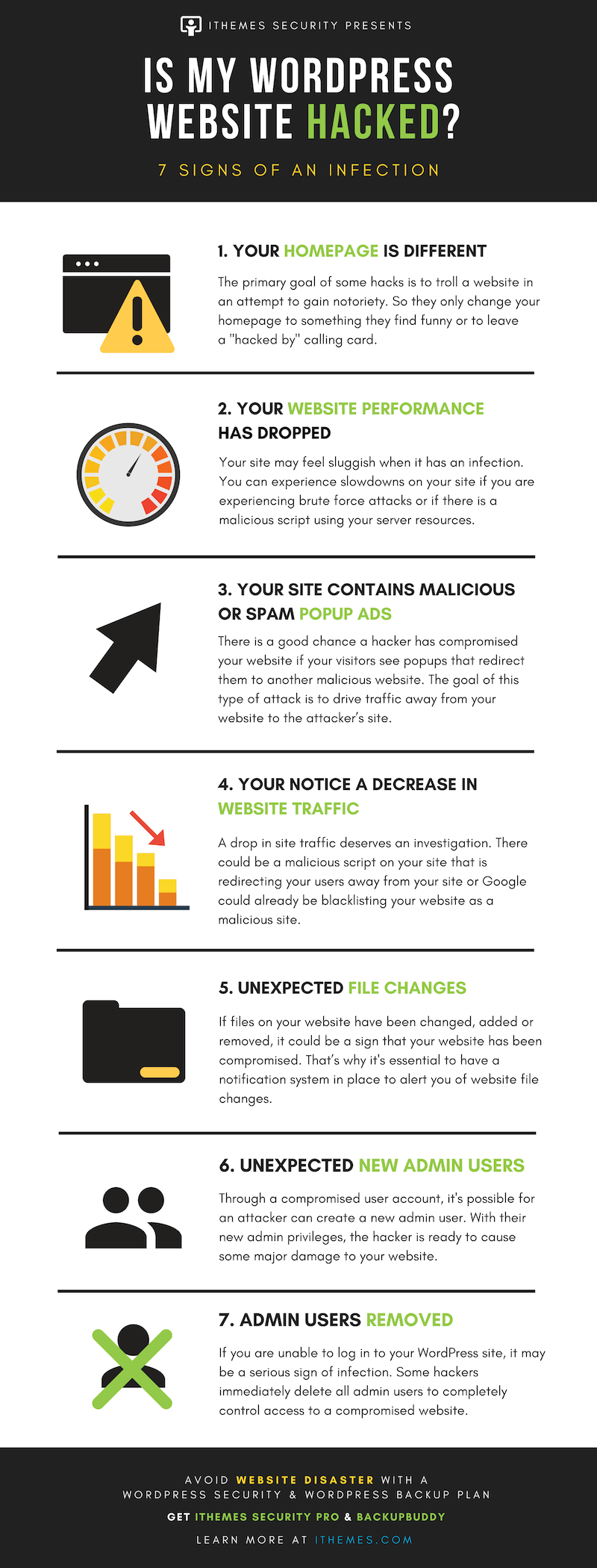
Finding yourself asking “Is my WordPress site hacked?” means you’ll want some quick answers. In this post, we cover seven signs of infection and what to do if you discover you’ve been hacked.
The faster you notice the signs of a website breach, the quicker you can get your site cleaned up. The quicker you can get your website cleaned, the less damage the hack can do to your website.
Note: Two things we mention quite a bit in this post is the importance of a solid WordPress backup and WordPress security solution. We highly recommend installing and activating a WordPress security plugin and WordPress backup plugin as soon as possible.
7 Signs Your WordPress Site Has Been Hacked
Not all hacks have the same goal, so the signs of a website compromise will depend on the attackers motive. Here are 7 different symptoms you need to look out for when you are monitoring the health of your site.
1. Your Homepage is Different
Changes to your homepage seem like an obvious sign. But how many times do you actually run a thorough check or your homepage? I know I typically go straight to my login URL and not my home URL. From there, I log in, update my site or edit a post. After I finish what I came to do, I often leave without looking at my website’s home page.
The primary goal of some hacks is to troll a website or gain notoriety. So they only change your homepage to something they find funny or to leave a hacked by calling card.
If you do notice a change to your homepage, you can restore your website quickly and easily using a backup file made with a trusted WordPress backup plugin such as BackupBuddy.
2. Your Website Performance Has Dropped
Your site may feel sluggish when it has an infection. You can experience slowdowns on your website if you are experiencing brute force attacks or if there is a malicious script using your server resources for cryptocurrency mining. Similarly, a DDoS (or denial of service attack) happens when a network of IPs simultaneously sends requests to your website in an attempt to cause it to crash.
If your site is running slowly, check the server access logs for an unexpected number of requests. You can also use a web application firewall like the one provided by Sucuri to help protect your website against a DDoS attack.
Just note that a drop in performance doesn’t necessarily mean someone hacked your site. You may just need some pointers for how to speed up a WordPress site with these WordPress optimization tips. The iThemes Security plugin’s WordPress Malware Scan feature will help to identify suspicious scripts.
3. Your Website Contains Malicious or Spam Popups Ads
There is a good chance a hacker has compromised your website if your visitors see popups that redirect them to a malicious website. The goal of this type of attack is to drive traffic away from your site to the attacker’s site so they can target users with spam or click fraud for Pay Per Click advertising.
The most frustrating thing about this type of hack is you may not be able to see the popups. A popup hack can be designed to not show for logged in users, which decreases the odds of website owners seeing them. So even when the site owner logs out, the popups will never display.
Your view of the popups can also be limited if you use an ad blocker extension in your browser. For example, a customer reported a popup hack and shared screenshots and a video of the popups. After I spent hours running through their website, I was not able to recreate anything they were reporting. I was convinced that their personal computer had been hacked and not the website. Finally, it dawned on me why I wasn’t able to see the popups. I had installed an ad blocker extension on my browser. As soon as I disabled the ad blocker extension, I was able to see popups everywhere. I share this embarrassing story to hopefully save you from running into the same mistake.
A WordPress security plugin such as iThemes Security plugin allows you to keep an eye on your website’s security logs for file changes, logins and changes made by users.
4. You Notice a Decrease in Website Traffic
If you log into your Google Analytics account and you notice a steep decline in website traffic, your WordPress site could be hacked. A drop in site traffic deserves an investigation. There could be a malicious script on your site that is redirecting visitors away from your site or Google could already by blacklisting your website as a malicious site.
The first thing you want to look for is your website’s outbound traffic. By tracking your website with Google Analytics, , you will need to configure your site to track the traffic leaving your site. The easiest way to monitor outbound traffic on your WordPress site is to use a WordPress Google Analytics plugin.
A good Google Analytics plugin will allow you to track specific activity with a click of a button.If you find your website has already been blacklisted by Google, follow these steps for how to remove Google blacklist warning.
5. Unexpected File Changes
If files on your website have been changed, added or removed, it could be a sign that your site has been compromised. That’s why it is essential to have a notification system in place to alert you of website file changes. You can investigate any unexpected changes by comparing the changed file to a version in a recent backup.The iThemes Security Pro File Change Scan feature will notify you of any changes made to your site.
Using a WordPress security plugin like iThemes Security can help you track file changes. Because of the number of notifications this setting can generate, you can exclude files and directories in the File Change Detection settings. It is okay to exclude directories that you know are going to be regularly updating. Backup and cache files are a perfect example of this and excluding them will reduce the number of notifications you will receive.
6. Unexpected New Users
If your website has any unexpected registrations of new admin users, that’s another sign your WordPress site has been hacked. Through an exploit of a compromised user, an attacker can create a new admin user. With their new admin privileges, the hacker is ready to cause some major damage to your site.
In November of 2018, we had several reports of new admin users being created on customer websites. Hackers used a vulnerability in the WP GDPR Compliance plugin (vulnerability patched in version 1.4.3) to create new admin users on WordPress sites running the plugin. The plugin exploit allowed unauthorized users to modify the user registration to change the default new-user role from a subscriber to an admin. Unfortunately, this wasn’t the only vulnerability and you can’t just remove the new users the attacker created and patch the plugin.
If you had WP GDPR Compliance and WooCommerce installed, your site might have been injected with malicious code. The attackers were able to use the WooCommerce plugin background installer to insert a backdoor installer in the database.If your site has a backdoor installed, you should contact a hack repair specialist. Another option is to use a backup file to roll back to a copy of your website prior to the breach using a previous backup.
7. Admin Users Removed
If you are unable to log into your WordPress site, even after a password reset, it may be a serious sign of infection.
When the Gentoo Github repo got hacked the first thing the attacker did was delete all admin users. So how did this hacker even get into their Github account? A Gentoo admin user’s password was discovered on a different site. I am guessing that the username and password was discovered either through scraping or a database dump. Even though the admin’s password for their Gentoo Github account was different than one used on the compromised account, it was very similar. So this would be like me using iAmAwesome2017 as a password on one account and iAmAwesome2019 on another site. So the hackers were able to figure out the password with a little effort.
As we can see, you should use a unique password for every account. A simple variation in your passwords isn’t enough. Using 1Password, you can generate and securely store strong, unique passwords for every site.
You can also enable the Trusted Devices feature in iThemes Security Pro to restrict admin capabilities for logins from untrusted devices. If an attacker successfully logs into your site as an existing admin user–either by a brute force attack or if the user’s credentials were part of a database dump–they will not have full admin capabilities.
[pullquote]Even with the password being compromised, this breach could have been prevented if the admin was using two-factor authentication. [/pullquote]
Two-Factor authentication requires an extra code along with your username and password credentials to log in. iThemes Security Pro allows you to enable WordPress two-factor using a mobile app or email to receive your access additional code.
Why Do Hackers Target WordPress Sites?
First, it’s important to understand that hackers aren’t only coming after sites that are built on the WordPress content management system. In fact, it’s safe to say that every site on the Internet, whether built with WordPress or not, has its own vulnerabilities and is open to the potential for hacking and other malicious attacks.
However, WordPress websites are the most common hacking target for one simple reason: WordPress is far and away the most used website building tool in the world. In fact, WordPress is currently powering 40% of all known websites.
This means that there are hundreds of millions of WordPress-powered websites currently flooding the Internet. The immense popularity of the WordPress platform gives hackers with evil intent a simple way to locate websites that lack proper security protocols, then exploit them for their own gain.
Hackers tend to have various different motives when they decide to hack into websites. Some hackers are just learning “the trade” and target websites that are the least secure and most vulnerable. Other hackers approach their efforts with highly malicious intent, such as distributing WordPress malware on your site or using your site to attack other unsuspecting websites.
Still other hackers use their efforts to spam unwanted information all over the Internet. Most of us have seen these kinds of spam messages in blog comment sections, or in our email boxes after a successful hack has exploited a site’s user email list.
By being able to get a hold of sensitive and private information, hackers can then sell it for an income or even hold the data ransom, essentially making people pay to get their information back in safe hands.
So, what’s the primary motivation of hackers? To create cash flow for themselves. The internet is a lucrative place that offers all walks of life the opportunity to generate a living wage. However, that doesn’t mean everybody goes about this in a legal, moralistic manner. A multitude of hackers are making high profits off of even the smallest website.
Money is all the motivation they need, but some enjoy the feeling of power they get when they successfully breach a website, but the vast majority are in the business solely for the cash.
What is a WordPress Vulnerability?
A WordPress vulnerability is a weakness or flaw in a theme, plugin, or WordPress core that can be exploited by a hacker. In other words, WordPress vulnerabilities create a point of entry that a hacker can use to pull off malicious activity.
Keep in mind that website hacking is almost all automated. Because of this, hackers can easily break into a large number of websites in virtually no time at all. Hackers use special tools that scan the internet, looking for known vulnerabilities.
Hackers like easy targets, and having a website that is running software with known vulnerabilities is like handing a hacker the step-by-step instructions to break into your WordPress website, server, computer, or any other internet-connected device.
Our weekly WordPress Vulnerability Report covers all of the publicly disclosed WordPress core, WordPress plugin, and WordPress theme vulnerabilities. In these reports, we share the name of the vulnerable plugin or theme, the affected versions, and the vulnerability type.
Common Methods Used to Hack into WordPress Websites
Hackers use vulnerable entry points to gain access to websites. These entry points include weak hosting servers, backdoors and even the WordPress login page via brute force attacks.
- Backdoors – Hackers can also create a website backdoor entry to your WordPress site. This means they create an entry point without needing to go through the standard WordPress login page. There are various ways to create a backdoor entry to gain unauthorized access to a WordPress site.
- Brute force attacks – This form of attack exploits the simplest method of gaining access to a site: by trying to guess usernames and passwords, over and over again, until they’re successful. WordPress sites are especially susceptible to brute force attacks by default because the system allows unlimited login attempts.
- Cross-site scripting – Cross-site scripting (XSS) is a type of malware attack that’s executed by exploiting cross-site vulnerabilities on any WordPress site. In fact, it’s the most common way for WordPress sites to be hacked because there are so many WordPress plugins that have XSS vulnerabilities.
- Remote code execution – The term remote code execution (RCE) refers to several different hacking techniques and cyberattacks, but they all have one major thing in common. RCE, sometimes referred to as code injection, is an increasingly common way for hackers to compromise websites of all kinds, including sites that run WordPress as their content management system.
- SQL injections – An SQL injection (SQLi) is an attack that allows a hacker to take advantage of a vulnerable SQL query to run their own query. SQL injections occur when an attacker is able to run their own SQL on a server.
Why Do WordPress Sites Get Hacked?
Several common reasons exist for why WordPress websites get hacked. Let’s unpack each of them.
Poor-Quality Hosting
Not all web hosts are created equal and choosing one solely on price can end up costing you way more in the long run with security issues. Most shared hosting environments are secure, but some do not properly separate users accounts.
Your host should be vigilant about applying the latest security patches and following other important hosting security best practices related to server and file security.
Just like with every other website in the world, sites running on the WordPress platform are all hosted on web servers. There are some hosting companies you may come across that don’t properly, or fully, secure their platform from malicious attacks.
If your site is hosted with an insecure hosting company, not only is your site open to the potential of hacks, but so is every other site hosted on their servers.
Choosing a quality WordPress hosting provider will help ensure that your website is safe and not open to hacking attempts that are out of your control. In fact, a server that has been properly secured will be able to block a lot of the most common WordPress hacking attempts before they ever become visible to you.
To get as much protection from hacks as you can get from your hosting provider, you may want to consider using a provider that offers a reliable Managed WordPress hosting plan.
Choose a reputable host for your website with a solid security record. Finding WordPress hosting that you can trust is the first of the WordPress security vulnerabilities you should try to mitigate.
Weak Passwords
Weak passwords are a hacker’s dream come true.
That’s why secure passwords are one of the biggest keys to keeping your WordPress site free of hacking success.
It’s critically important that you use very unique and strong passwords for each of the accounts below. Any one of them could allow a hacker with bad intentions to gain access to your site and cause harm to your reputation and brand:
- Any and all WordPress administrator accounts
- Your website hosting control panel, or cPanel, account
- All FTP accounts
- The WordPress database that’s used to power your website
- All email accounts that are used for your hosting account or WordPress admin
Every single one of these key accounts is password-protected and needs to have a unique and unbreakable password applied.
When you use weak passwords that can easily be guessed, it makes it quite simple for malicious hackers to crack your passwords wide open using very basic hacking tools available to almost everybody with an Internet connection.
This major problem can be easily avoided simply by using strong passwords that are completely unique for each one of these account logins.
If you don’t already have one, consider installing a reliable password manager that can help you keep all of your passwords up-to-date without needing to write them all down in a notebook. Of course, if you’re struggling to come up with strong and unique passwords, you can also use a built-in strong password generator or Google the term “unbreakable password generator” to find various free online tools that can help you out.
Keep in mind that your WordPress login is the most commonly attacked WordPress security vulnerability because it provides the easiest access to your site’s admin page. Brute force attacks are the most common method of exploiting your WordPress login.
[pullquote] A brute force attack is an attempt to correctly guess username and password combinations to gain access to the backend of your WordPress site. [/pullquote] Brute force attacks can be effective because WordPress doesn’t limit the number of login attempts someone can make.
You can strengthen the security of your WordPress login by using a WordPress security plugin like iThemes Security Pro to limit the number of login attempts. Limiting login attempts is just the first step in WordPress brute force protection.
Being mindful of your WordPress password security is also essential in securing your WordPress login, and this is why you should use a password manager to generate random strong passwords and securely store them. Forcing every WordPress user on your site to use a strong password will greatly decrease the effectiveness of a brute force attack.
Not Updating WordPress Core, Themes & Plugins
When your WordPress site is running outdated versions of plugins, themes or WordPress, you run the risk of having known exploits on your site.
The fastest way to a hacked WordPress site is through outdated and vulnerable plugins, themes, or WordPress core versions.
WordPress updates are not just for new features or bug fixes; they can also include security patches for known exploits. Even though this is the easiest of the WordPress security vulnerabilities to prevent, most successful hacks use exploits that are found in outdated software.
There’s a strange fear in the world of WordPress development among many site owners. For some reason, a lot of WordPress users are afraid to update their sites to the most current version of WordPress. The fear, it seems, is that in running an update to WordPress core they run the risk of breaking their sites and losing all of their work. Run a backup before updating uncase there is an issue, but keep in mind the fastest way to WordPress hacked is through outdated plugins, themes, or WordPress core.
The reality is that every new WordPress version is designed to fix bugs and further secure you from vulnerabilities and the potential for hacks. In fact, if you haven’t been keeping your WordPress software fully updated, you’re actually leaving your site far more vulnerable to trouble than you are by avoiding the updates.
If you have a fear that running an update will cause harm to your site or break it completely, it’s important to run a WordPress backup plugin that can instantly restore your site if the worst possible situation happens.
BackupBuddy is one of the best, and easiest, solutions for keeping your WordPress site fully backed up at all times. If anything goes wrong or your site breaks for any reason, you can quickly bring back the previous version and start over.
You can automate updates on your site Using the iThemes Security Pro WordPress version management feature. Automating your updates ensures you get the critical security patches that protect your site against WordPress security vulnerabilities and as a bonus, it reduces the amount of time you spend maintaining your WordPress site.
In a similar way as we just discussed with keeping your WordPress core software constantly updated to the current version, the same holds true for the themes and plugins that you’re running on your site.
In fact, keeping themes and plugins fully updated is equally important as updating WordPress. If you’re using a theme or plugin that’s outdated from current WordPress security fixes, your entire site is more vulnerable to malicious hacking attempts.
Security bugs and flaws are discovered in themes and plugins on a daily basis. Typically, the authors of the themes and plugins you use quickly release these fixes and make them available to you. However, if you choose not to update the software when you’re alerted that a change has been made available, there’s not a lot the developers can do for you.
It’s important to keep all of your WordPress plugins and themes up-to-date at all times. And again, if you’re worried that an update could cause an internal conflict and break your site, BackupBuddy has you fully covered.
Not Using Two-Factor Authentication
In addition to using strong passwords, adding WordPress two-factor authentication is one of the best methods to secure your site’s logins. Two-factor authentication requires users to use an authentication token in addition to their username and password to login to WordPress.
Even if a correct username and password are phished directly from a user’s email, the malicious login attempt can still be prevented if the user is using the mobile application to receive their authentication token. Two-factor authentication adds an incredibly strong layer of security to your WordPress site, and can easily be added using a plugin like iThemes Security.
In fact, recent research from Google confirms using two-factor authentication can stop 100% of automated bot attacks. I like those odds. iThemes Security Pro makes it easy to add two-factor authentication to WordPress websites.
Installing Software From Untrusted Sources
A quick Google search will uncover dozens of websites throughout the web that try to distribute premium or paid WordPress themes and plugins completely free of charge. Of course, it’s easy to be tempted to download and install those free “nulled” themes and plugins on your site to save some money.
But downloading nulled WordPress plugins and themes from these highly unreliable sources is extremely dangerous to the health of your site. Not only will they likely compromise your site security, but they can easily be used by hackers to steal highly sensitive information.
Remember to only download themes and plugins from those most reliable sources, such as directly from the developers who created them or from the official WordPress repository.
If you’re not able to afford the cost of a premium product or simply don’t want to buy one, there are thousands of free and reliable themes and plugins that you can choose from. While the free versions may not pack as much of a punch as the paid versions, they can still help you accomplish what you want to do and keep your site safe from attack.
You may even be able to find discount codes on some popular (and safe) paid themes and plugins if you take a little time to look.
Only install WordPress plugins and themes from trusted sources.
You should only install software that you get from WordPress.org, well-known commercial repositories or directly from reputable developers. You will want to avoid “nulled” version of commercial plugins because they can contain malicious code. It doesn’t matter how you lock down your WordPress site if you are the one installing malware.
If the WordPress plugin or theme isn’t being distributed on the developer’s website, you will want to do your due diligence before downloading the plugin. Reach out to the developers to see if they are in any way affiliated with the website that is offering their product at a free or discounted price.
In addition, avoid using abandoned WordPress plugins. If any plugin installed on your WordPress site has not received an update in six months or longer, you may want to make sure it hasn’t been abandoned. A plugin not having any recent updates doesn’t necessarily mean it has been abandoned, it could just mean it is feature complete and will only receive updates to ensure compatibility with the latest versions of WordPress and PHP.
Running a Non-SSL Website
When someone visits your WordPress site, a line of communication between their device and your server begins. The communication isn’t a direct line, and the information passed between the visitor and your server makes several stops before being delivered to its final destination.
To better understand how encryption works, consider how your online purchases get delivered. If you’ve ever tracked delivery status, you have seen that your order made several stops before arriving at your home. If the seller didn’t properly package your purchase, it would be easy for people to see what you purchased.
When a visitor logs into your WordPress site and enters payment information, this information isn’t encrypted by default. So just like your unpackaged purchase, there is an opportunity for the login credentials and credit card details to be discovered at every stop between the visitor’s computer and your server.
Luckily, unencrypted communication is one of the easiest WordPress security vulnerabilities to mitigate.
Adding an SSL certificate to your is a great way to encrypt and package the communication on your site to ensure that only the intended recipients can view the sensitive information being shared. Your host may provide a service to add an SSL certificate to your WordPress site or you can add the SSL certificate on your own.
If you decide to go the do-it-yourself route, I would recommend using certbot. Certbot makes it very easy to add a Let’s Encrypt certificate to your site as well as set it up to automatically renew your SSL certificate. You can also check out our WordPress HTTPS training to learn how to add an SSL certificate to your website.
My WordPress Site Has Been Hacked – Now What?
The scenario we’re looking at is when one (or more) of a theme’s template files have been injected with malicious code. Such code can then affect (and infect) other theme files, or in fact, any other file on the server. On a shared hosting account, this could mean that your site can be infected through another site hosted on the same server. Now that’s a scary thought.
- Go through all the files in your WordPress installation to make sure that there is no script still remaining on the site that continues to inject malicious code at different intervals.
- Change all FTP, cPanel, all WordPress passwords, and your WordPress salts and keys. If the attack happened because the attacker got ahold of any of your admin login credentials and you do not change them, there is nothing to prevent them from automatically modifying files again at a later date.
- Do a comprehensive scan of all systems that connect to your server (via FTP or other methods). There are viruses floating around that can sniff login details. So, even if you change all your passwords, if just one system is compromised with such a virus, all the servers/sites connected to that system will continue to get attacked.
- If you have a WordPress backup that you made before the hack, you might try restoring from that backup, checking the files to see if the hack is in place, and go from there.
- Thoroughly clean every one of your sites. Don’t just remove one infected file modification or run a scanner plugin. Go through every directory on your site and look for suspicious files. You may want to talk to your hosting company and/or hire a consultant such as Sucuri to help with this process. If even one compromised file or covertly-placed script remains on the site, this can be used by the attacker to automatically compromise your site all over again.
Protect and Secure Your WordPress Website from Being Hacked
Knowing how dangerous it can be if your website is compromised can be the catalyst you need to start implementing your WordPress security strategy. Here are 7 important tips to protect your site from being hacked.
1. Update your plugins, themes, and WordPress version as soon as possible.
Updates aren’t just for cool new features and bug fixes. Plugin and them updates can include critical security patches for known vulnerabilities. Keep your site safe and updated.
2. Use Two-Factor Authentication for your WordPress admin login.
In this blog post, New research: How effective is basic account hygiene at preventing hijacking, Google stated that using two-factor authentication can stop 100% of automated bot attacks. iThemes Security Pro makes it easy to add two-factor authentication to WordPress websites.
3. Don’t allow users to use compromised passwords.
A data breach is typically a list of usernames, passwords, and often other personal data that was exposed after a site was compromised. Refusing to let your website’s users use passwords that have been known to be compromised can drastically increase the security of your site. You can easily refuse compromised passwords using iThemes Security Pro.
4. Only install software from trusted sources.
You should only install software that you get from WordPress.org, well known commercial repositories, or directly from reputable developers. You will want to avoid “nulled” versions of commercial plugins because they can contain malicious code. It doesn’t matter how you lock down your WordPress site if you are the one installing malware.
Plugins and themes from unknown sites can be compromised with code that gets the ball rolling for the hackers. Some plugin/theme viruses are designed to automatically infect every other plugin and theme on the site. This means that even if you clean up the one that caused the problem, the others are still infected.
5. Add website security logging.
WordPress security logs provide detailed data and insights about activity on your WordPress website. If you know what to look for in your logs, you can quickly identify and stop malicious behavior on your site. Learn how to add WordPress security logs to your website.
6. Have a backup plan (and make it reliable).
Backup your WordPress site early, and backup often. Having a healthy full backup of your site is key. Keep an archive of several backup files. If disaster strikes, you will need a backup to restore you site (after the server is cleaned). Quick tip on backup files: run some test restores of your backup files every now and then. Having a backup that you can’t restore is probably the worst thing that can happen (after being hacked). BackupBuddy is a WordPress backup plugin that enables you to set scheduled backups that will run unattended, and where backup files can be saved to a remote location. This should offer you peace of mind that you will always have a healthy backup file.
7. Install a WordPress security plugin.
A WordPress security plugin like iThemes Security Pro offers 30+ ways to secure and protect your website from common WordPress security vulnerabilities. With WordPress two-factor authentication, brute force protection, strong password enforcement and more, you can add an extra layer of security to your website.
Wrapping Up
Because a hacked WordPress website can cause serious damage, advanced steps must be taken to prevent your site from being compromised. This article explored common ways to secure a WordPress site and shared you some basic steps you can take to ensure you never end up with a hacked WordPress site.
Fortunately, WordPress owners can protect themselves from falling victim to a hacked site. By taking preventative action and securing your website against the possibility of a hack, you’ll be protecting the investment of both time and money you’ve made into your website.
Solid Security is part of Solid Suite — The best foundation for WordPress websites.
Every WordPress site needs security, backups, and management tools. That’s Solid Suite — an integrated bundle of three plugins: Solid Security, Solid Backups, and Solid Central. You also get access to Solid Academy’s learning resources for WordPress professionals. Build your next WordPress website on a solid foundation with Solid Suite!
Sign up now — Get SolidWP updates and valuable content straight to your inbox
Sign up
Get started with confidence — risk free, guaranteed