WordPress Vulnerability Report: June 2021, Part 4
Vulnerable plugins and themes are the #1 reason WordPress websites get hacked. The weekly WordPress Vulnerability Report powered by WPScan covers recent WordPress plugin, theme, and core vulnerabilities, and what to do if you run one of the vulnerable plugins or themes on your website. Each vulnerability will have a severity rating of Low, Medium, High, or Critical.

Vulnerable plugins and themes are the #1 reason WordPress websites get hacked. The weekly WordPress Vulnerability Report powered by WPScan covers recent WordPress plugin, theme, and core vulnerabilities, and what to do if you run one of the vulnerable plugins or themes on your website.
Each vulnerability will have a severity rating of Low, Medium, High, or Critical. Responsible disclosure and reporting of vulnerabilities is an integral part of keeping the WordPress community safe. Please share this post with your friends to help get the word out and make WordPress safer for everyone.
Get SolidWP tips direct in your inbox
Sign up
Get started with confidence — risk free, guaranteed
WordPress Core Vulnerabilities
WordPress Plugin Vulnerabilities
1. BCS BatchLine Book Importer

Plugin: BCS BatchLine Book Importer
Vulnerability: Unauthenticated Product Import
Patched in Version: 1.5.8
Severity: High
2. WP SVG Images
Plugin: WP SVG Images
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 3.4
Severity Score: Medium
3. Vik Rent Car
Plugin: Vik Rent Car
Vulnerability: CSRF to Stored XSS
Patched in Version: 1.1.7
Severity Score: High
4. WP FoodBakery
Plugin: FoodBakery
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: 2.2
Severity Score: Medium
5. wpForo Forum

Plugin: wpForo Forum
Vulnerability: Open Redirect
Patched in Version: 1.9.7
Severity Score: Medium
6. WooCommerce Stock Manager

Plugin: WooCommerce Stock Manager
Vulnerability: CSRF to Arbitrary File Upload
Patched in Version: 2.6.0
Severity Score: High
7. Smooth Scroll Page Up/Down Buttons
Plugin: Smooth Scroll Page Up/Down Buttons
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: No known fix
Severity Score: Medium
8. Request a Quote
Plugin: Request a Quote
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 2.3.4
Severity Score: Medium
9. WP YouTube Lyte
Plugin: WP YouTube Lyte
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 1.7.16
Severity Score: Medium
10. WP JobSearch
Plugin: WP JobSearch
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 1.7.4
Severity Score: Medium
11. WP Reset
Plugin: WP Reset
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 1.90
Severity Score: Medium
12. Backup by 10Web
Plugin: Backup by 10Web
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: No known fix – plugin closed
Severity Score: High
13. W3 Total Cache
Plugin: W3 Total Cache
Vulnerability: Authenticated Stored Cross-Site Scripting
Patched in Version: 2.1.3
Severity Score: Medium
14. WP Fluent Forms
Plugin: WP Fluent Forms
Vulnerability: Cross-Site Request Forgery
Patched in Version: 3.6.67
Severity Score: High
15. Advanced AJAX Product Filters
Plugin: Advanced AJAX Product Filters
Vulnerability: Unauthenticated Reflected Cross-Site Scripting
Patched in Version: 1.5.4.7
Severity Score: High
16. Filebird
Plugin: Filebird
Vulnerability: Unauthenticated SQL Injection
Patched in Version: 4.7.3
Severity Score: High
17. 404 to 301

Plugin: 404 to 301
Vulnerability: Broken Access Control
Patched in Version: 3.0.8
Severity Score: Medium
WordPress Theme Vulnerabilities
1. Jannah

Theme: Jannah
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: 5.4.5
Severity Score: High
2. FoodBakery
Plugin: FoodBakery
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: 2.2
Severity Score: Medium
A Note on Responsible Disclosure
You might be wondering why a vulnerability would be disclosed if it gives hackers an exploit to attack. Well, it is very common for a security researcher to find and privately report the vulnerability to the software developer.
With responsible disclosure, the researcher’s initial report is made privately to the developers of the company that owns the software, but with an agreement that the full details will be published once a patch has been made available. For significant security vulnerabilities, there may be a slight delay in disclosing the vulnerability to give more people time to patch.
The security researcher may provide a deadline for the software developer to respond to the report or to provide a patch. If this deadline is not met, then the researcher may publicly disclose the vulnerability to put pressure on the developer to issue a patch.
Publicly disclosing a vulnerability and seemingly introducing a Zero-Day vulnerability–a type of vulnerability that has no patch and is being exploited in the wild– may seem counterproductive. But, it is the only leverage that a researcher has to pressure the developer to patch the vulnerability.
If a hacker were to discover the vulnerability, they could quietly use the Exploit and cause damage to the end-user(this is you), while the software developer remains content on leaving the vulnerability unpatched. Google’s Project Zero has similar guidelines when it comes to disclosing vulnerabilities. They publish the full details of the vulnerability after 90 days whether or not the vulnerability has been patched.
How to Protect Your WordPress Website From Vulnerable Plugins and Themes
As you can see from this report, lots of new WordPress plugin and theme vulnerabilities are disclosed each week. We know it can be difficult to stay on top of every reported vulnerability disclosure, so the iThemes Security Pro plugin makes it easy to make sure your site isn’t running a theme, plugin or WordPress core version with a known vulnerability.
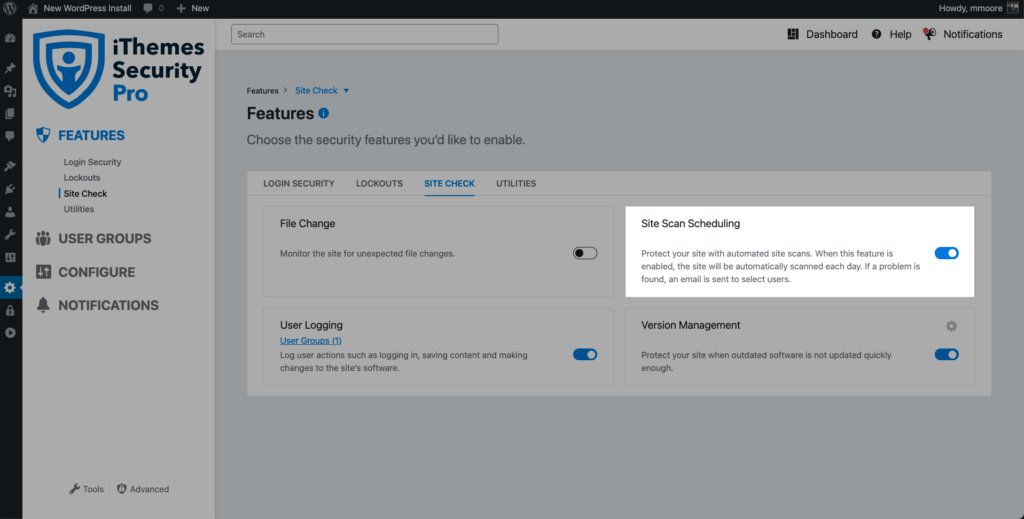
1. Turn on the iThemes Security Pro Site Scanner
The iThemes Security Pro plugin’s Site Scanner scans for the #1 reason WordPress sites get hacked: outdated plugins and themes with known vulnerabilities. The Site Scanner checks your site for known vulnerabilities and automatically applies a patch if one is available.
To enable the Site Scan on new installs, navigate to the Site Check tab on the Features menu inside the plugin and click the toggle to enable the Site Scan.
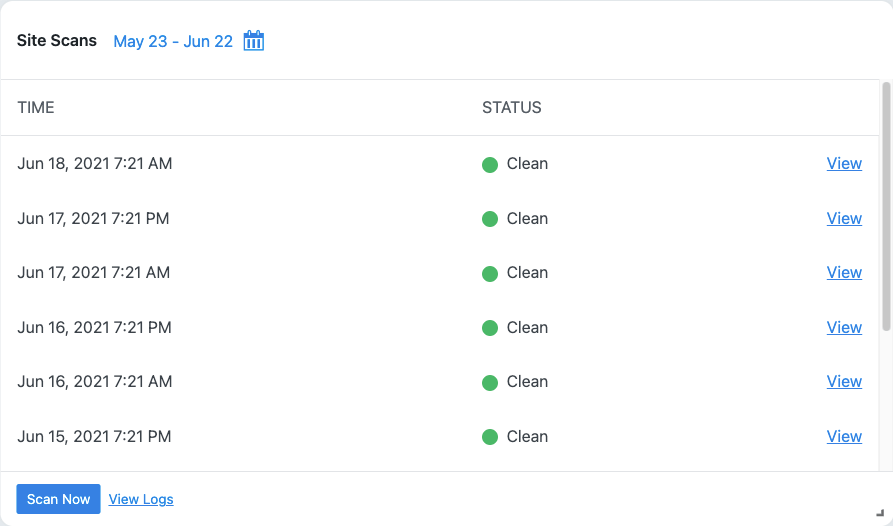
To trigger a manual Site Scan, click the Scan Now button on the Site Scan Security Dashboard card.
If the Site Scan detects a vulnerability, click the vulnerability link to view the details page.
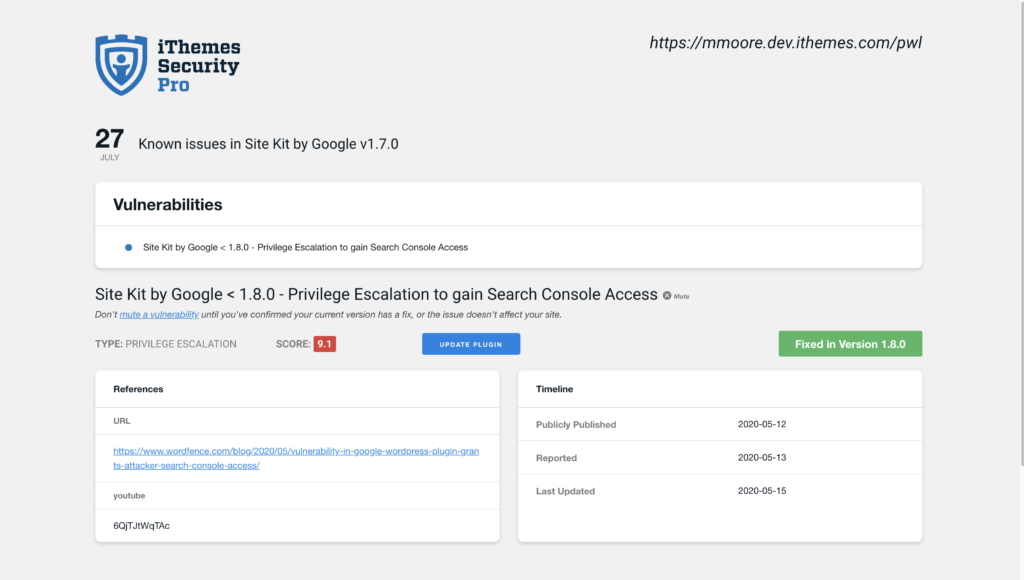
On the Site Scan vulnerability page, you will see if there is a fix available for the vulnerability. If there is a patch available, you can click the Update Plugin button to apply the fix on your website.
2. Turn on Version Management
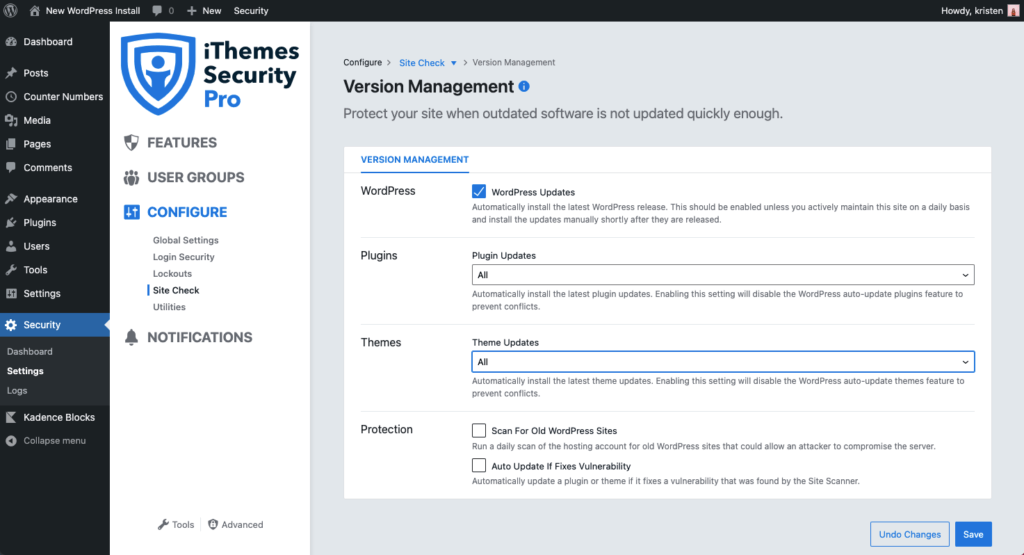
The Version Management feature in iThemes Security Pro integrates with the Site Scan to protect your site when outdated software is not updated quickly enough. Even the strongest security measures will fail if you are running vulnerable software on your website. These settings help protect your site with options to update to new versions automatically if a known vulnerability exists and a patch is available.
From the Settings page in iThemes Security Pro, navigate to the Features screen. Click the Site Check tab. From here, use the toggle to enable Version Management. Using the settings gear, you can configure even more settings, including how you want iThemes Security Pro to handle updates to WordPress, plugins, themes, and additional protection.
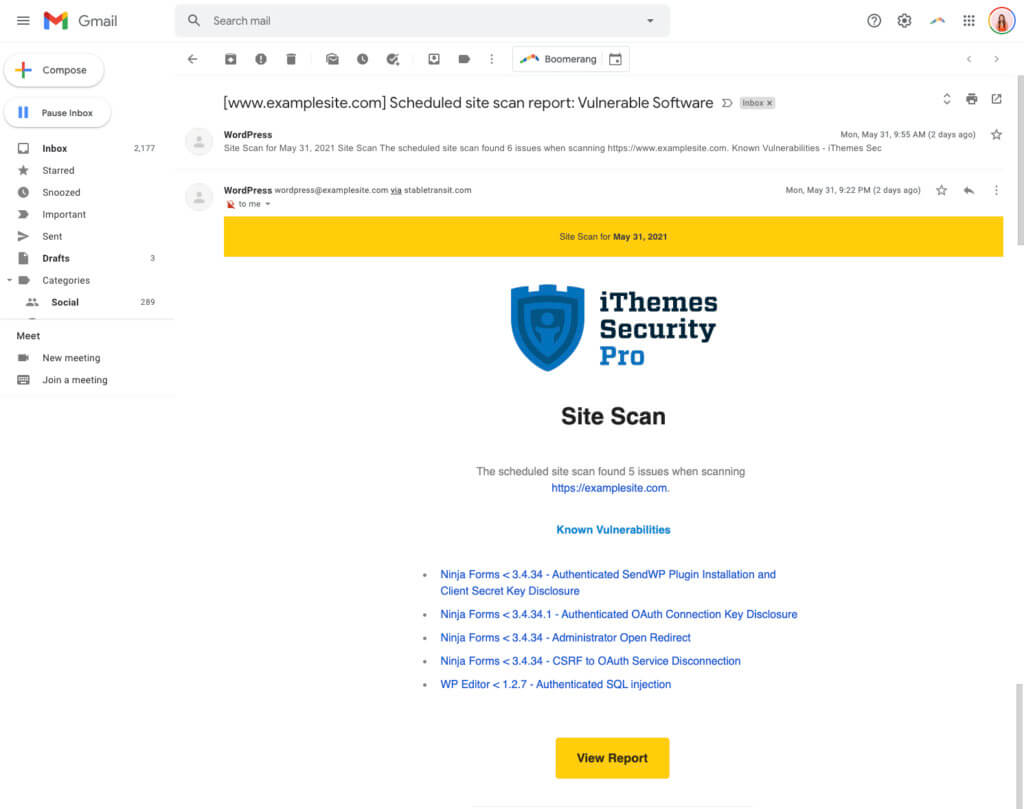
3. Get an Email Alert When iThemes Security Pro Finds a Known Vulnerability On Your Site
Once you’ve enabled Site Scan Scheduling, head to the Notification Center settings of the plugin. On this screen, scroll to the Site Scan Results section.

Click the box to enable the notification email and then click the Save Settings button.
Now, during any scheduled site scans, you’ll get an email if iThemes Security Pro discovers any known vulnerabilities. The email will look something like this.

Get iThemes Security Pro Today!
7.0 is Here + 30% Off!
iThemes Security Pro, our WordPress security plugin, offers 50+ ways to secure and protect your website from common WordPress security vulnerabilities. With WordPress, two-factor authentication, brute force protection, strong password enforcement, and more, you can add an extra layer of security to your website.
This week, we’re celebrating the release of iThemes Security Pro 7.0 with a sale so you can upgrade all your sites to Pro. Just use coupon code 7POINTOH at checkout on any new iThemes Security Pro purchase* through June 30, 2021.
Get iThemes Security Pro
Sign up now — Get SolidWP updates and valuable content straight to your inbox
Sign up
Get started with confidence — risk free, guaranteed